
Zero Trust Architecture: Security Beyond the Perimeter
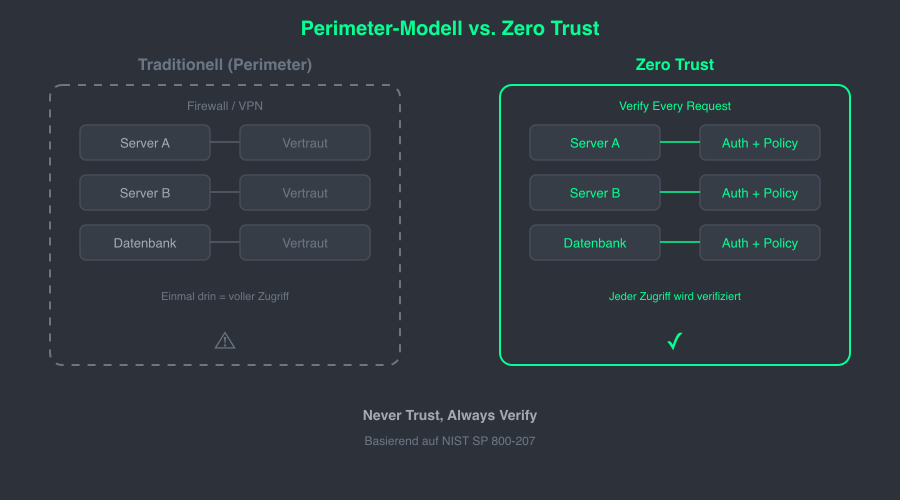
Traditional security models rely on a simple principle: trust everything inside the network, verify everything outside. In an era of remote work, cloud migration, and increasing supply chain attacks, this approach is no longer sufficient. Zero Trust Architecture (ZTA) inverts this model entirely.
What is Zero Trust?
Zero Trust is a security paradigm built on the principle of "Never trust, always verify". No user, device, or network segment receives implicit trust - regardless of location. NIST Special Publication 800-207 defines the reference framework for implementation and describes three core logical components:
- Policy Engine (PE) - makes access decisions based on policies, risk scores, and identity data
- Policy Administrator (PA) - translates Policy Engine decisions into concrete actions
- Policy Enforcement Point (PEP) - enforces access decisions at the network boundary
Core Principles and Implementation
The three core principles of Zero Trust are:
- Verify Explicitly - Every request is evaluated based on identity, device health, location, and behavioral patterns
- Least Privilege Access - Access is granted only to the extent required for the specific task
- Assume Breach - The system assumes an attacker is already inside the network and minimizes the blast radius
In Kubernetes environments, Zero Trust can be implemented through NetworkPolicies. These enforce microsegmentation at the pod level:
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: allow-frontend-to-backend
namespace: production
spec:
podSelector:
matchLabels:
app: backend
policyTypes:
- Ingress
ingress:
- from:
- podSelector:
matchLabels:
app: frontend
ports:
- protocol: TCP
port: 8080
This policy permits only traffic from frontend pods to the backend on port 8080. All other inbound traffic is implicitly blocked.
Why This Matters
The ongoing migration of workloads to the cloud and the spread of hybrid work models render the traditional network perimeter obsolete. Zero Trust addresses this reality by binding security to identities and policies rather than network boundaries. With growing support from CNI technologies such as Calico and Cilium, implementation in containerized environments is becoming increasingly practical.